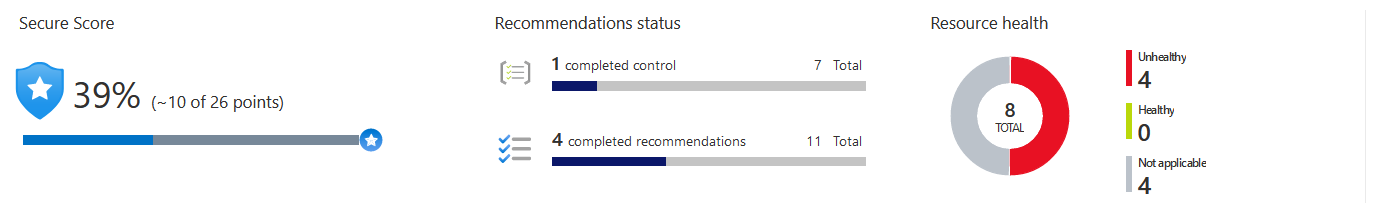
Security Hygiene, Azure Security Center, and Secure Score
The basics
Let's start this article with some basic cybersecurity terminology. Security hygiene, or cyber hygiene, is a general term used to describe the ongoing practice of keeping your technology and IT estate in a healthy and protected state. The metapho...
Read More